DIAGNOSIS
The diagnosis aims to analyze the essential points of IT structures and build a complete technical documentation of the system. For this, the following points are considered:
• System information
• Current status and usefulness of the system in the business
• Current support and versions for hardware, operating systems, database and application
• Data and user security
• Performance and frequent errors at runtime
• Network connectivity and relationship with satellite systems
• Settings and parameterizations
• Quality of application developments
• Architecture and Governance
This report provides recommendations on how to manage your Infrastructure, Database and Applications, regardless of its technology, identifying the weaknesses and risks of the system, bringing opportunities for improvement, putting itself at the center and communicating with the needs of different specialties.
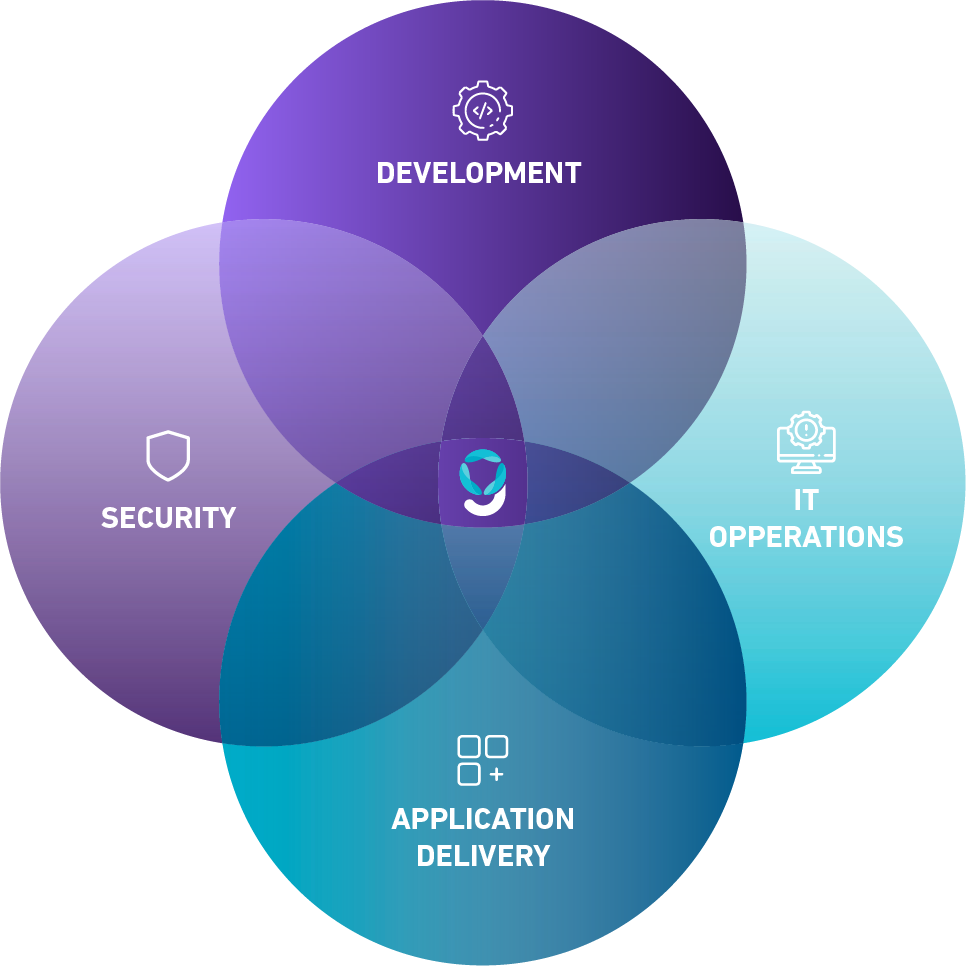
INFORMATION SECURITY MANAGEMENT
The construction of adequate security makes it possible to minimize the risk of data loss, leakage and data hijacking, thus ensuring the reliability of your systems and processes. For this, it is necessary to understand how your company’s security works and prepare a plan that allows you to work on security at all its levels, focusing on three main pillars:
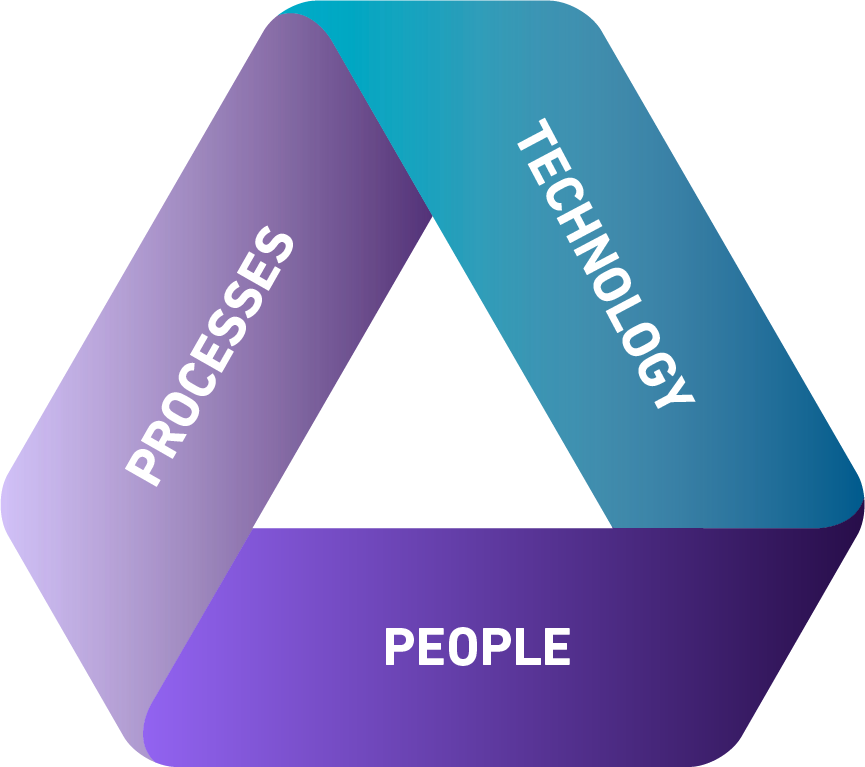
Technology: Aims to establish a technological plan that allows you to improve the maturity of the security of your company’s systems, focusing on protecting your infrastructure, networks, database and applications, treating different internal and external vulnerabilities that can compromise integrity, confidentiality and availability.
Processes: Its objective is to map the processes of each business area to define a risk matrix together with the rules for the segregation of functions for each position/area, as well as its functionalities.
People: Aims to train and raise awareness of people who have access to technologies in order to establish system operation standards for each business process.
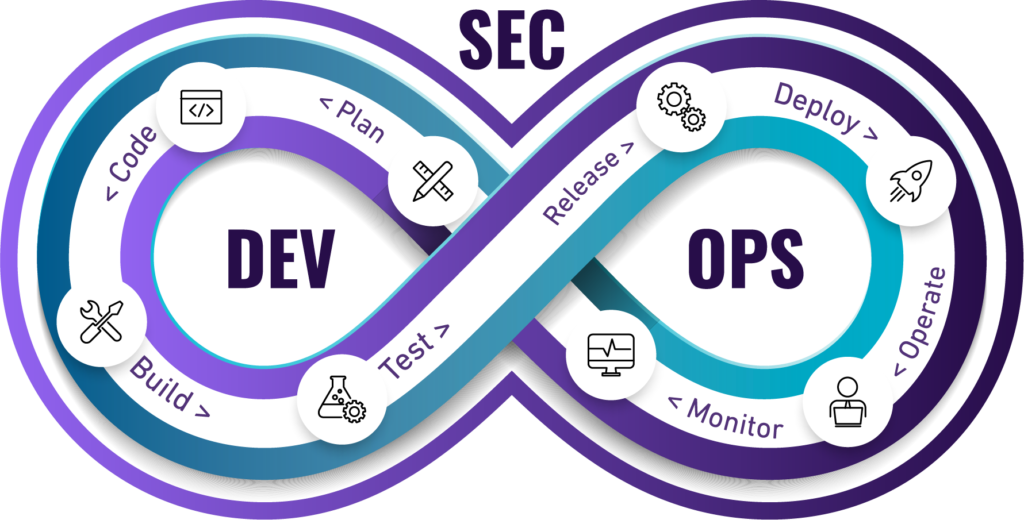
APPLICATION DEVELOPMENT
Your organization may require your applications to have new development adjustments to meet a new reality or demand, such as:
• Integrations
• New features
• New services
• Improvements
Properly built applications allow your organization to optimize time and effort, ensuring stable, high-performance and safe operation.
SPECIAL OPERATIONS
A special operation arises when a company faces a one-off event that can lead to damage, whether by a threat or a critical incident.
All companies are susceptible to crisis and, when this happens, it is important to have experts who are able to carry out a “top to bottom” analysis of the situation: detect the root cause of the problem, define and execute a correction plan in a short time. time and re-establish the business operation, thus minimizing financial losses.

SUPPORT
In the support model of your IT, it is important not to limit yourself to acting an eventuality, it is necessary to act on the root cause of the incidents, carry out crisis management, analyze the risks and define an assertive action plan. It should also clarify doubts in a flexible way, be adaptable to your company’s culture and allow you to simplify change management through a basic structure, maintaining a history of maintenance and documentation.
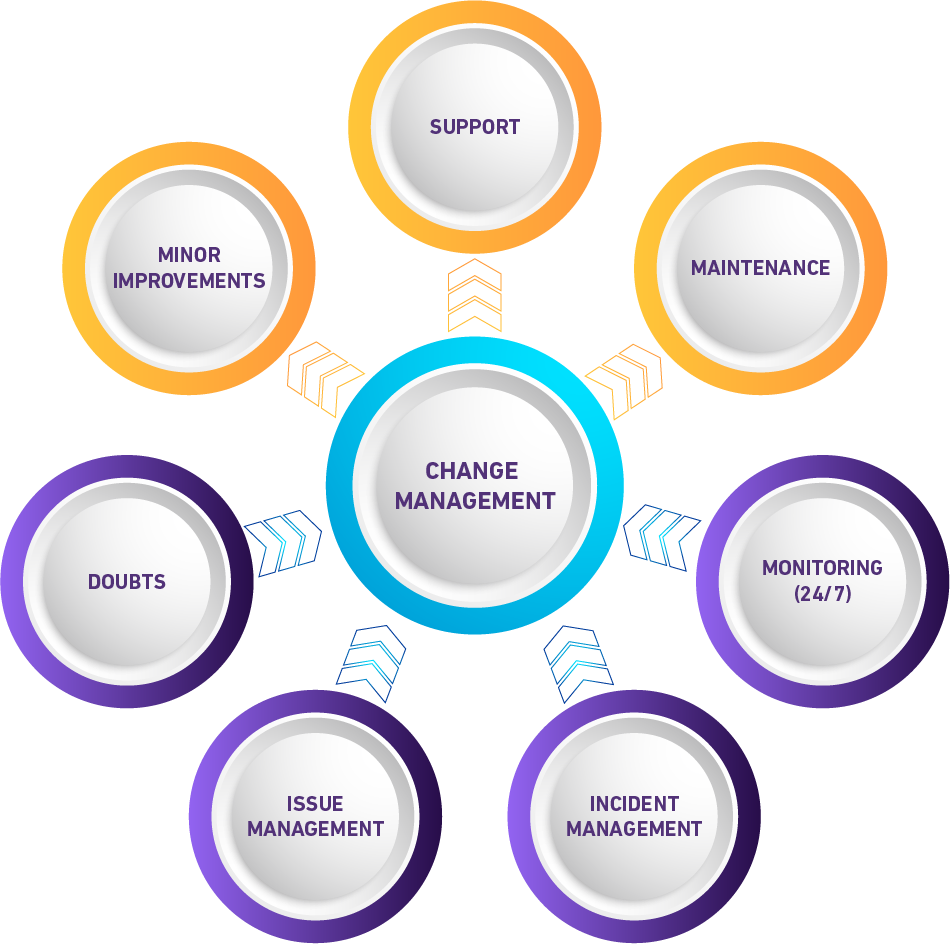
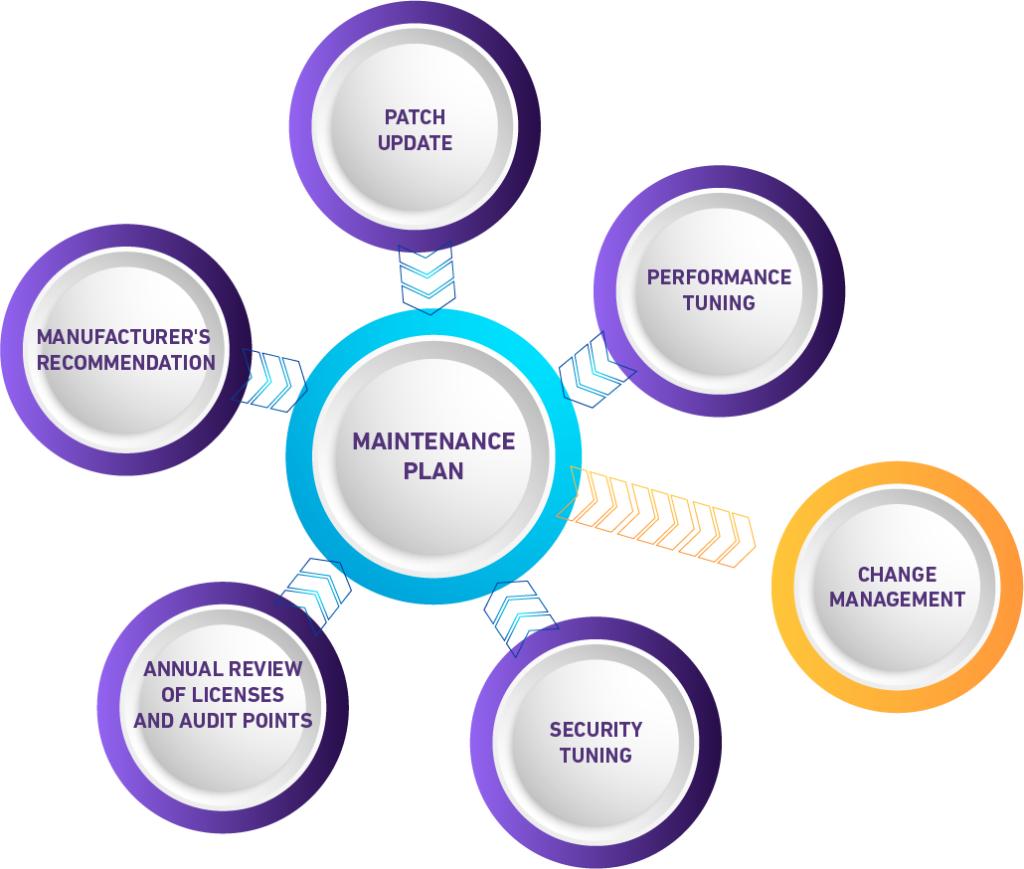
On the other hand, it is important to proactively anticipate avoidable incidents by implementing an annual/routine maintenance plan tailored to your business. You must keep your systems within the manufacturers’ recommendations, checking the latest version releases and considering performance and security. It is important that the model is preventive and has a minimum structure that offers predictability, confidence and stability to your business.
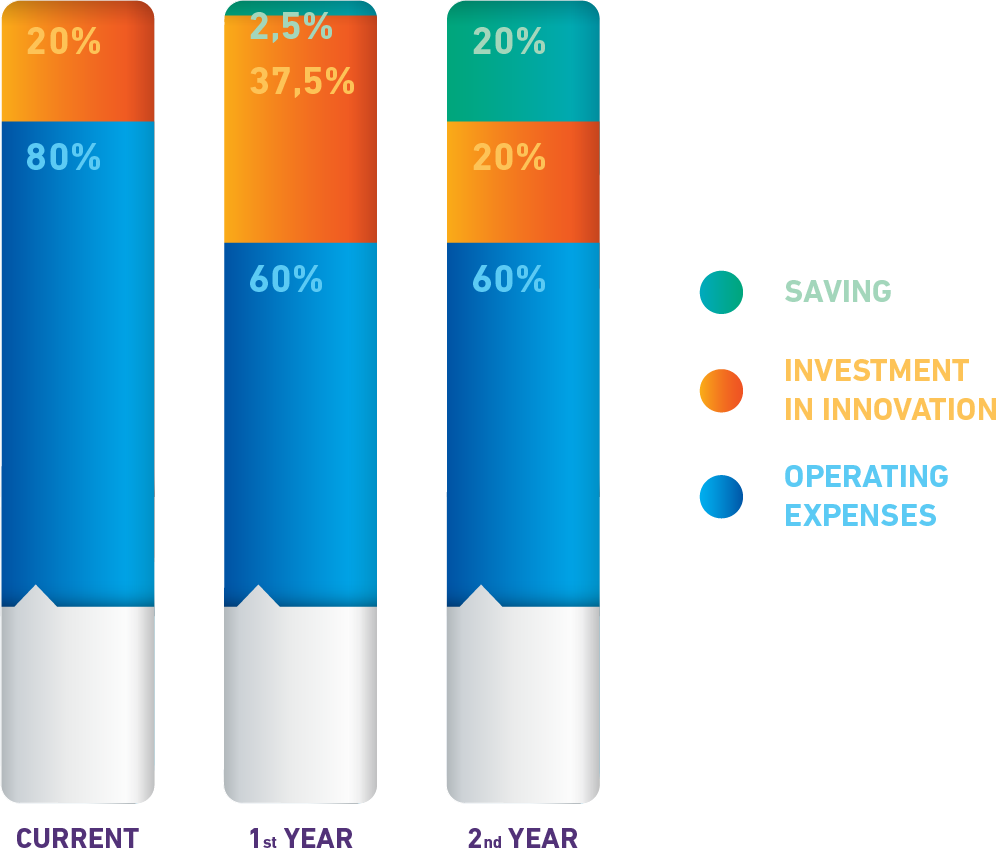
CLOUD SERVICES
If you’re thinking about moving your IT to the cloud, you need to think about advanced and emerging technologies that will allow you to scale your business to make the most of your technology investments. Market statistics show that when an organization moves its IT to the cloud, they are able to free up capital to invest in innovation activities. This means that the IT budget does not increase, maintenance is done normally but, at the same time, it becomes more economical because of the cloud, being a prerequisite of the digital transformation.
For this, it is necessary to establish a gradual and orderly migration plan, which allows your organization to take a leap in technologies without impacting the current operation, boosting your IT.
CUSTOMIZED ARCHITECTURE
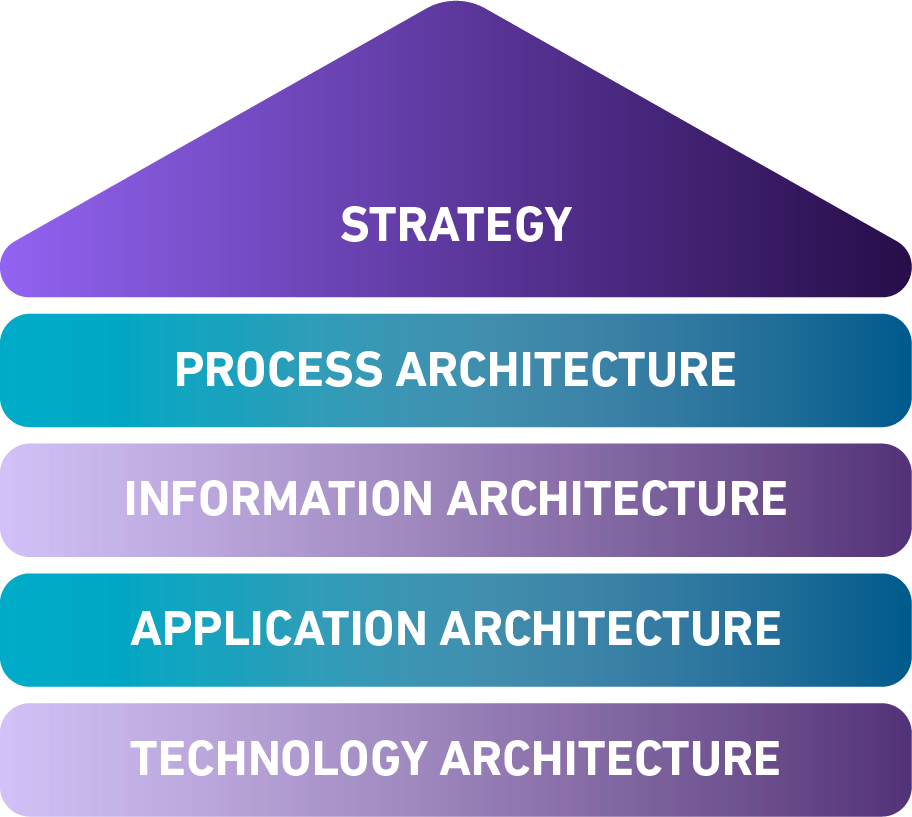
The purpose is to ensure that the resources invested are used in the best way, minimizing cost and maximizing use. When you build a bespoke architecture, it positively impacts the performance of your technologies and applications, as well as the structure of your processes and data, bringing competitive advantages to your organization. This allows your IT to evolve intelligently and agilely, meeting business demands more efficiently.

